Base Bridge Security: What’s Really Under the Hood in 2026
The first impression of the Base bridge is almost disarming: a clean interface, a Coinbase-branded on-ramp, and a user experience that feels much closer to a centralized exchange transfer than to a complex cross-chain operation. Under that smooth exterior, however, sits one of the most consequential pieces of infrastructure in the Base ecosystem – the canonical bridge between Ethereum mainnet and Base.
At a distance, it looks like “just another rollup bridge.” A closer examination reveals something more nuanced: a security model inherited from the OP Stack, strong alignment with Ethereum’s security guarantees, and a still-evolving decentralization and fault-proof story that matters for anyone moving serious capital. Over time, on-chain metrics and the absence of catastrophic incidents through late 2024 pushed the assessment from cautious skepticism to measured confidence – but with very specific caveats around governance and fast-bridge usage.
1. Executive Summary
This review evaluates the security of the Base canonical bridge – the primary pathway for assets moving between Ethereum and Base — as of the most recently available public information (through late 2024), and extrapolates the structural implications that remain highly relevant in 2026. It focuses on the protocol mechanics, not on individual front-end implementations or third-party bridges.
- Security model: The Base bridge inherits the Optimism/OP Stack architecture: assets are custodied in Ethereum L1 contracts, with Base functioning as an optimistic rollup. This gives it fundamentally stronger guarantees than multi-signature or wrapped-token bridges, but also imports OP Stack’s still-maturing fault-proof ecosystem and upgrade governance.
- Code maturity: The bridge contracts are relatively lean, heavily reused from the OP Stack, and widely audited. This reduces novel attack surface but concentrates systemic risk: a flaw in OP Stack bridge logic would affect multiple L2s.
- Operational posture: Coinbase’s involvement brings professional-grade operational security and monitoring, but also reinforces centralization and upgrade-key trust assumptions in the short to medium term.
- Risk concentration: Direct use of the canonical bridge is comparatively robust; the more acute tail risks for users in practice come from fast-bridge and liquidity-network layers on top, which often introduce additional trust assumptions.
- Ecosystem impact: The bridge is the primary capital ingress for Base and underpins the chain’s liquidity profile and MEV dynamics. Its reliability has been a key factor in Base’s rapid growth relative to other OP Stack chains.
Overall, the Base canonical bridge compares favorably against many cross-chain alternatives, but its real-world security profile is ultimately a blend of Ethereum settlement assurances, OP Stack fault-proof maturity, and Coinbase-governed upgrade controls. For sophisticated users in 2026, understanding where they are trusting code and where they are trusting institutions remains essential.
2. Protocol Overview
Base is an Ethereum Layer 2 network built on the OP Stack, positioning itself as a secure, low-cost environment closely integrated with Coinbase products. The Base canonical bridge is the official, protocol-level mechanism for moving ETH and ERC-20 tokens between Ethereum L1 and Base L2.
- Directionality:
- L1 → L2 deposits: Users lock assets in Ethereum L1 bridge contracts and receive corresponding balances on Base.
- L2 → L1 withdrawals: Users burn or escrow assets on Base, then finalize withdrawals on Ethereum after an on-chain challenge period.
- Core contracts:
- On Ethereum L1: contracts analogous to OptimismPortal and L1StandardBridge hold funds and manage cross-domain messages.
- On Base L2: corresponding L2StandardBridge and message-passing contracts mint, burn, or release tokens according to verified state roots.
- Security model:
- Funds ultimately sit in Ethereum contracts; Base’s consensus and sequencing cannot arbitrarily seize L1 funds without passing through the canonical exit process.
- The integrity of exits relies on the correctness of posted state roots and the ability of fraud proofs (fault proofs) to challenge invalid ones within a specified window.
This is in contrast to many earlier-generation bridges (e.g., multi-sig custodial bridges or generic message-passing protocols) where a small validator set or off-chain key compromise could directly drain funds. Base’s design is far closer to Arbitrum’s canonical bridge and the broader optimistic rollup family than to standalone cross-chain bridges like Multichain, Nomad, or Poly Network, which have historically been frequent exploit targets.
3. Technical Analysis
3.1 Architecture and Innovation
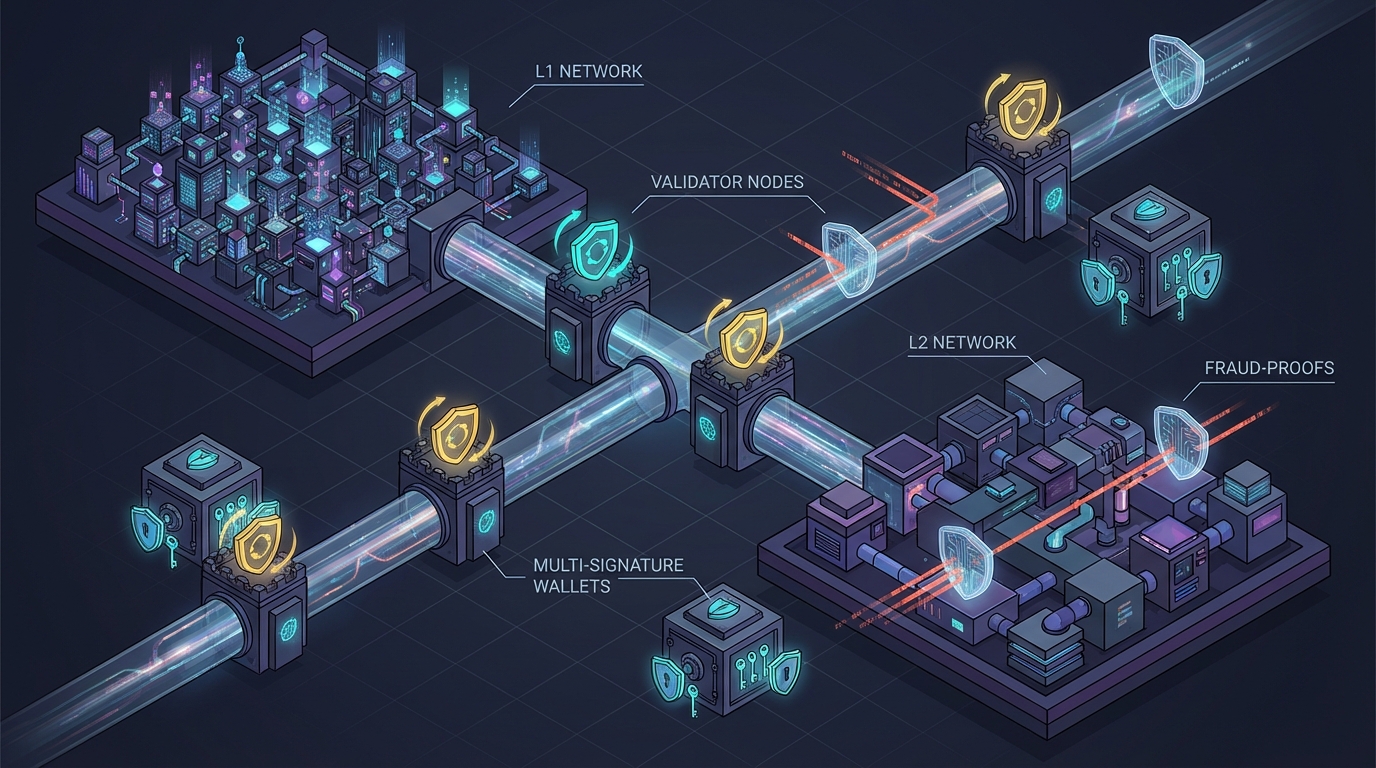
The Base bridge leverages the OP Stack’s modular design. At a high level, the architecture consists of:
- Data availability layer: Transaction data is posted to Ethereum, allowing for independent reconstruction of Base’s state from L1 data.
- State commitment: A designated L2 output proposer posts state roots (checkpoints of Base’s state) to Ethereum.
- Fraud/fault proof pipeline: A mechanism (evolving over time) allows challengers to dispute invalid state roots within a challenge window, reverting fraudulent outputs.
- Bridge/message layer: Cross-domain messages (deposits, withdrawals, contract calls) are executed only when the relevant state transitions are considered final, after any disputes.
From a security perspective, the key innovation is not Base-specific but rather the OP Stack’s gradual shift toward permissionless, trust-minimized fault proofs. Earlier OP Stack deployments relied on centralized or semi-centralized guardians; over time, more generalized and open proof systems have been rolling out. Base’s bridge security trajectory follows this evolution closely, with the long-term goal of minimizing governance discretion in the validation of L2 state roots.
3.2 Smart Contract Design
The smart contracts underlying the Base bridge are designed with minimalism in mind: they primarily handle escrow, accounting, and message validation rather than complex business logic. Key design characteristics include:
- Escrow-based custody: L1 contracts escrow canonical assets (ETH and ERC-20s) and track corresponding L2 representations. For standard tokens, the model is straightforward lock-and-mint / burn-and-release.
- Standardized interfaces: The bridge uses standardized interfaces for ERC-20s, and an extensible pattern for token mapping, which simplifies audits and integration.
- Restricted surface area: Logic is focused on:
- Validating cross-domain message proofs
- Preventing replay attacks
- Enforcing challenge periods
- Emitting canonical events for infrastructure and monitoring
- Upgradability: Some components of the OP Stack bridge architecture are upgradable via governance-controlled proxies. This is both a security tool (rapid patch capability) and a risk factor (upgrade key compromise or malicious governance).
Because the Base bridge reuses widely deployed OP Stack contracts rather than novel, bespoke code, its risk profile is somewhat inverted compared to many DeFi protocols. It takes on systemic risk (shared with Optimism and other OP Stack chains), but benefits from a broader community of auditors, white-hats, and users actively probing the same code paths.
3.3 Scalability Considerations
Bridges are usually not the primary throughput bottleneck on an L2, but their design still affects scalability and user experience:
- Deposit throughput: L1 → L2 deposits are limited mostly by Ethereum block space and gas prices. In high-stress periods, batched transactions and aggregator services can mitigate UX friction.
- Withdrawal latency: L2 → L1 exits for canonical security must respect the full challenge window (typically several days for optimistic rollups). This is a design choice favoring security over speed and leads to the proliferation of fast-bridge services offering quick but trust-augmented exits.
- Eventual batching: Internally, bridge operations can be batched and optimized, but the security model hinges on final settlement on Ethereum rather than on any off-chain or L2-only mechanism.
Relative to alternatives, Base’s bridge is not unusually scalable or constrained; it sits in the same design space as Arbitrum and Optimism’s canonical bridges. Performance improvements are more likely to come from Ethereum scaling and EIP-level optimizations than from radical changes in bridge logic.
3.4 Integration Capabilities
Integration is one of Base’s defining strengths, and the bridge is central to this:
- Wallets and interfaces: Major wallets and on-ramps integrate Base bridging as a first-class option, often abstracting away the underlying canonical bridge calls.
- Centralized exchange routing: Coinbase can route user funds directly to Base, functionally substituting for a manual bridge transaction for many retail users. While this is not “bridge usage” in a narrow technical sense, it reduces pressure on the public bridge UI and can smooth demand spikes.
- Third-party fast bridges: Protocols like Hop, Across, and others (where supported) typically rely on the canonical bridge as the ultimate settlement layer, building liquidity and routing logic on top. This layered design means the Base canonical bridge is a substrate for an entire bridging ecosystem.
In practice, this integration richness improves usability but can obscure risk boundaries: many users think they are “using the Base bridge” when in fact they are using a fast bridge or centralized off-ramp that settles through it. For security analysis, keeping that distinction crisp is crucial.
4. Market Analysis
4.1 Adoption Metrics
By late 2024, Base had emerged as one of the larger L2s by total value locked and transaction volume, driven by Coinbase’s user base and a strong DeFi and NFT ecosystem. While precise 2026 bridge metrics depend on up-to-date on-chain data, several structural patterns have been clear:
- High share of canonical flows: A significant portion of net new capital to Base has historically come via the canonical Ethereum bridge, especially for institutional or high-value transfers that prioritize security over speed.
- Growing fast-bridge layer: Over time, a rising share of smaller, retail-sized transfers has moved to fast-bridge protocols, which settle against the canonical bridge but add distinct counterparty risks.
- Sticky liquidity: Once capital reaches Base, liquidity tends to circulate within the L2 rather than frequently exiting back to L1, a sign that users view Base as a long-term operating environment, not just a temporary side-chain.
The stability and perceived safety of the canonical bridge are a precondition for this behavior. A major canonical bridge incident would likely have systemic consequences far beyond immediate losses, affecting Base’s positioning in the L2 race.
4.2 Competitive Landscape
From a user’s perspective in 2026, Base’s bridge competes on three primary axes: security model, speed, and ecosystem gravity.
- Versus other L2 canonical bridges (Arbitrum, Optimism, zkSync, Scroll, Linea):
- Security assumptions are similar for optimistic rollups (Base/Optimism/Arbitrum): Ethereum as settlement layer, challenge windows, and governance-controlled upgrades.
- zk-rollups (zkSync, Scroll, Linea) emphasize validity proofs over fraud proofs, trading off different trust assumptions and operational complexity.
- Base does not stand out as radically more or less secure at the protocol level; the differentiator is Coinbase’s operational and ecosystem weight.
- Versus cross-chain bridges and message protocols (LayerZero, Wormhole, Axelar, etc.):
- Base’s canonical bridge is narrower in scope but more Ethereum-native in its guarantees.
- Generic cross-chain messaging often involves validator sets or guardians whose compromise can cause global, multi-chain damage — a different and often higher-risk profile.
Put simply, Base’s bridge is not “innovative” in a marketing sense; it is intentionally conservative, sticking close to Ethereum rollup best practices and leveraging OP Stack standardization. In security-critical infrastructure, that conservatism is a feature, not a bug.
4.3 Revenue Model Viability
The Base bridge itself is not primarily a revenue engine. Fees paid on L1 (gas) go to Ethereum validators, and L2 fees are driven by broader usage, not bridge transactions alone. However, it contributes indirectly to Base’s economics:

- Sequencer revenue: More capital on Base leads to more on-chain activity and more sequencer-derived fees and MEV opportunities.
- Ecosystem expansion: A safe and reliable canonical bridge lowers friction for major projects and liquidity providers to deploy on Base, enhancing the network effect.
- Coinbase synergies: By making Base accessible and credible as an L2 destination, the bridge reinforces Coinbase’s broader strategy of embedding onchain experiences into its product suite.
Thus, bridge security is less about driving direct income and more about protecting the long-term value of the Base ecosystem and its alignment with Ethereum.
5. Risk Assessment
5.1 Security Audits and Track Record
The OP Stack bridge components used by Base have undergone multiple audits by reputable firms and benefit from continuous peer review as they are shared across Optimism and other L2s. Up to late 2024, there were no publicly disclosed catastrophic exploits of the canonical Base bridge.
That said, the absence of incidents does not imply the absence of vulnerabilities. Bridges have historically been some of the highest-value targets in crypto, with several billion dollars lost across the ecosystem in exploits involving design flaws, key compromises, or integration errors. Base’s relative safety so far is more a reflection of conservative design and careful operations than of invulnerability.
5.2 Centralization and Governance Concerns
The most material non-technical risk factor is centralization.
- Upgrade keys: Governance-controlled proxies and upgrade authorities can, in principle, modify bridge behavior. While these controls are intended for emergency patches and protocol evolution, they also represent a trust assumption: users must believe that upgrade keys will not be misused or compromised.
- Sequencer and proposer: As long as the sequencer and state root proposer are relatively centralized (with Coinbase and/or a small set of entities), there exists a window in which collusion plus a flawed or disabled fault-proof system could approve invalid states, at least temporarily.
- Emergency controls: Some deployments maintain “pause” or “circuit breaker” functionality in case of detected issues. These can prevent further damage but also reinforce the need to trust the controlling entities.
In practice, this centralization risk is somewhat mitigated by Coinbase’s strong brand incentives and regulatory scrutiny, but from a purist, trust-minimized perspective, it remains a critical part of the security model. The trajectory toward more decentralized fault proofs and multi-party governance will determine how this risk profile evolves through 2026 and beyond.
5.3 Economic and Design Vulnerabilities
Beyond pure contract correctness, several economic and design-layer risks affect Base bridge usage:
- Challenge window risk: During the withdrawal challenge period, user funds are in a liminal state. While the security model assumes honest challengers will detect invalid state roots, a failure of monitoring or collusion could, in a worst case, enable fraudulent exits or censorship.
- Fast-bridge dependencies: Many users interact with Base through fast exits that rely on liquidity providers or off-chain guarantees. The failure or insolvency of these intermediaries is not a failure of the canonical bridge, but it is a real risk experienced by end users who may not distinguish between the layers.
- MEV and sandwiching: Large bridge transactions can be attractive MEV targets, particularly when token prices shift between L1 and L2. Front-running or sandwiching attacks can degrade execution prices or create adverse selection for liquidity providers.
- L1 contagion: Because the bridge sits on Ethereum, extreme Ethereum-level events (consensus failures, extended finality issues, or governance shocks) would propagate directly to Base’s settlement and, by extension, to the bridge.
These are not unique to Base, but they shape the risk/reward calculus for different categories of users: casual retail users, DeFi protocols, market makers, and institutional allocators will each prioritize different aspects.
5.4 Team and Governance
Base is developed by a team with deep ties to Coinbase and the Optimism ecosystem. On the positive side, this means professional engineering practices, strong incident response capabilities, and clear communication channels. On the cautionary side, it reinforces a governance structure that is not yet fully decentralized or community-driven.
For high-stakes bridge users in 2026, practical due diligence still includes:
- Reviewing the current state of OP Stack fault proofs and whether they are fully permissionless or still guarded.
- Understanding who currently controls bridge-related upgrade keys and emergency powers.
- Monitoring Base and Optimism governance forums for proposals affecting bridge parameters or security assumptions.
6. Ecosystem Impact
6.1 Value to Base Users
The canonical bridge is the foundational artery of capital into Base. Its existence and reliability directly affect:
- User confidence: Knowing that inbound capital ultimately resides in Ethereum contracts with rollup-style guarantees encourages both retail and institutional participation.
- Protocol design space: DeFi protocols on Base can assume relatively robust L1 settlement properties, enabling more sophisticated collateralization and risk management frameworks compared to sidechains with weaker security models.
- Developer adoption: Builders choosing a home L2 care deeply about “can my users exit safely?” The Base bridge provides a credible answer aligned with Ethereum norms.
6.2 Synergies with Other Protocols
The bridge catalyzes multiple layers of ecosystem activity:
- Liquidity networks: Fast-bridge and cross-chain liquidity providers build on the canonical bridge as their settlement backbone.
- Restaking and security markets: Ethereum-aligned security primitives (e.g., restaking, shared security services) can be extended to Base via the canonical bridge’s message pathways.
- Cross-L2 arbitrage: Traders bridge assets between L2s (Base ↔ Optimism ↔ Arbitrum) using the respective canonical bridges and aggregators, aligning Base more tightly with the broader rollup ecosystem.
These synergies make the Base bridge more than a simple on/off ramp; it is a hub in a growing network of rollup-native capital flows.
6.3 Long-Term Sustainability and Innovation Contribution
From a long-term perspective, the Base bridge’s greatest contribution is its participation in a shared, open-source rollup stack. Improvements to OP Stack fault proofs, bridge efficiency, and monitoring benefit not just Base, but every chain adopting the stack — and vice versa.

Sustainability here is so multi-layered:
- Base benefits from Optimism’s research and development on fault proofs and security improvements.
- Optimism benefits from Base’s scale, which stress-tests and validates the stack in production.
- Ethereum benefits from an L2 ecosystem that increasingly converges on battle-tested patterns for bridging and settlement.
In 2026, the most meaningful “innovation” around Base bridge security is likely to be less about flashy new primitives and more about incremental, shared hardening: better monitoring, more robust fault proofs, clearer disclosures, and progressive decentralization of control.
7. Investment Perspective
7.1 Token Economics and Value Capture
Base does not have a native token, and the canonical bridge does not directly accrue protocol fees in the way that many DeFi protocols do. Instead, value capture happens indirectly via:
- ETH and stablecoins bridged to Base powering DeFi yield opportunities.
- Sequencer revenue (ultimately benefiting stakeholders in the Base operating entity and, indirectly, Coinbase’s broader strategy).
- Improved liquidity and user retention on Base, which may benefit protocols and assets deployed on the L2.
For investors, the bridge is therefore more of a systemic risk factor than a direct yield source: its failure would be catastrophic to the network’s value, while its smooth functioning is a baseline assumption baked into any investment thesis on Base-native assets.
7.2 Growth Potential
Growth for the Base bridge is effectively growth in:
- Total value locked moving through the bridge over time.
- Diversity and depth of assets bridged (beyond ETH and major stablecoins).
- Institutional adoption of Base as a primary execution venue, which typically involves sizable, security-sensitive bridging flows.
If Base continues to gain share among L2s, the bridge’s strategic importance will only increase — and so will attacker incentives. From an investment and risk management standpoint, this underscores the need to continuously reassess assumptions about fault proofs, governance decentralization, and operational controls.
7.3 Risk/Reward Profile for Users and Protocols
Different actors face distinct risk/reward trade-offs when engaging with the Base bridge in 2026:
- Retail users: For occasional deposits and long-term use of Base, the canonical bridge offers a strong security profile relative to most third-party bridges. The main “cost” is slow withdrawals if using the canonical path.
- DeFi protocols: Protocols holding significant treasuries on Base must treat the canonical bridge and underlying OP Stack security as key infrastructure dependencies, monitoring governance changes and proof system upgrades closely.
- Liquidity providers and market makers: Participants in fast bridges and cross-L2 arbitrage strategies must layer canonical-bridge risk with counterparty and liquidity risks from the additional protocols they use.
For all of these groups, the Base canonical bridge is near the “conservative end” of the bridging risk spectrum, particularly when compared to multi-chain, validator-set-based messaging protocols. But conservative does not mean risk-free, and governance centralization remains the central caveat.
8. Verdict
Stepping back, Base’s canonical bridge is best understood not as a flashy standalone protocol, but as a carefully engineered component of a broader Ethereum-aligned rollup stack. It is structurally closer to Arbitrum’s and Optimism’s canonical bridges than to the more fragile cross-chain bridges that have dominated exploit headlines.
On the strengths side:
- Assets custodied in Ethereum L1 contracts with well-understood security assumptions.
- Leverage of the OP Stack codebase, benefiting from shared audits and community scrutiny.
- Professional operations and monitoring, rooted in Coinbase’s infrastructure experience.
- Deep integration across wallets, exchanges, and fast-bridge protocols, making the canonical bridge a foundational settlement layer.
On the weaknesses and watchpoints side:
- Ongoing centralization in upgrade governance, sequencer control, and, historically, fault-proof activation.
- User confusion between canonical bridge guarantees and the additional risks of fast bridges and centralized routing.
- Systemic exposure to any latent vulnerabilities in the OP Stack bridge design shared across multiple L2s.
For Base ecosystem participants in 2026, the practical conclusion is nuanced:
The Base canonical bridge, standing on Ethereum and the OP Stack, offers one of the more robust and conservative paths for moving value into and out of an L2 environment. It is a defensible choice for users and protocols that prioritize security and Ethereum alignment over absolute speed. However, its safety is not a given; it is a function of continuing progress on decentralized fault proofs, transparent governance, and disciplined operational practices.
In other words, the machinery under the hood is solid by current industry standards — but it still demands informed trust and ongoing scrutiny from anyone betting serious capital on the future of Base.
